One of the most important places for cybersecurity is within the healthcare system. As a healthcare professional, you work with sensitive data — and there are strong repercussions for both your business and its patients should a breach occur. This year, we’ve seen hundreds of healthcare data breaches that exposed 500 or more records (U.S. Department of Health and Human Services, n.d.).
As a result, cybersecurity is one of the most significant components of compliance with the Health Insurance Portability and Accountability Act (HIPAA). Strong cybersecurity practices are essential for avoiding the pitfalls that come with a data breach, like fines, a damaged reputation, patient identity theft, and even legal repercussions. Read more about cybersecurity in healthcare environments and what you need to know to protect your practice.
What is Healthcare Cybersecurity?
This is a complex topic with many branches, aspects, and threats. Common healthcare system elements include charting, billing, electronic prescriptions, administration, operations, third-party partnerships, and more. These operations may be based on-site or in the cloud, sharing networks with peripheral devices, medical equipment, and other components. As a result, healthcare systems need defenses against potential cybersecurity threats.
The most common cause of data breaches in the healthcare industry for 2021 was misdelivery due to human error (Verizon, 2021). Both internal actors and accidental loss of data are damaging. This form of breach doesn’t require advanced knowledge of the inner internet technology (IT) workings of the facility — just an authorized user and a convincing email.
But human errors are far from the only concern. If a disgruntled employee decides they want to steal patient information, they may be able to when the proper security measures aren’t in place. Another unforeseeable incident that could create issues would be a natural disaster, such as a flood that renders your building’s computer systems useless.
As digital tools become more necessary and patients demand convenience, cybersecurity risks grow for organizations of all sizes. That said, small healthcare practices often have more cause for concern, with fewer IT resources available to mitigate problems. Ultimately, in the cybersecurity industry, it’s not a question of “if” an attack happens but “when.” For healthcare providers, putting robust cybersecurity protections into place can help keep everyone’s information safe.

The Benefits of Cybersecurity in the Healthcare Industry
While many think of cybersecurity as a component of HIPAA compliance, it has far more relevance to your practice than simply meeting regulatory requirements. Strong healthcare cybersecurity can help you do the following:
- Maintain a trustworthy reputation: If your practice is exposed to a data breach, it can face extensive reputational damage. No matter the measures you take afterward, patients may associate you with poor data management and turn to other providers. For most healthcare practices, trust is a fundamental component of maintaining a good public image. By avoiding breaches and solidifying trust, you can retain and attract patients.
- Avoid financial issues and other penalties: Between fines, settlements, lost revenue, and the mediation requirements of a data breach, your practice can endure numerous financial issues when it experiences a data breach. Severe violations can even come with criminal penalties. Implementing necessary precautions helps authorities see how you’re protecting patient data by complying with HIPAA regulations.
- Improve technological adoption and efficiency: New technology enters the healthcare field every year. Strong cybersecurity protection gives you a safer space to add new equipment and software and reap the benefits these improvements have to offer. From improved data collection via remote monitoring devices to modern flexibility from your payment platform, improving cybersecurity protection enables you to make the changes you want with greater peace of mind.
Healthcare Cybersecurity Statistics
While cybersecurity is a must-have, many healthcare organizations don’t prioritize it, leaving data security to fall through the cracks. Here are some eye-opening statistics about cybersecurity in healthcare and in general:
- The average cost of managing a healthcare data breach rose to an average of $9.42 million in 2021 (HIPAA Journal, 2021).
- Organizations further along in a cloud modernization plan were able to detect and respond to breaches an average of 77 days faster. (IBM, 2021).
- The cost of a breached record in healthcare was higher than in other industries from 2010 to 2019 — $429 per record in healthcare vs. $150 per record overall (Seh et al., 2020).
Therefore, we can see just how important cybersecurity is when we look at what happens when it’s not a high priority. A data breach isn’t uncommon or cheap, so prioritizing your approach to cybersecurity is essential.
Threats Facing Healthcare Cybersecurity
Healthcare cybersecurity threats can come in many forms. These threats include:
- Malware: Malware is a wide-reaching term that encompasses software and files with malicious intent. The user may click on a link in an email or visit a website that launches a download automatically. These items often infect a victim’s computer without their knowledge or consent, accomplishing tasks like stealing credentials, using up device resources, or corrupting files. For example, ransomware can leave files and systems unusable until the victim pays a ransom. In healthcare, it could bring operations to a halt and disrupt vital patient care.
- Phishing: Phishing is usually done via email and involves tricking the recipient into completing a task, such as initiating a money transfer, submitting credentials to a scammer, or clicking on a link that downloads malware.
- Data exposure: In the last section, we mentioned how data breaches often come from external attacks, but they can also occur from less malicious sources, such as a lost laptop or unintentional disclosure from an employee.
- Insider threats: No business owner can overlook the possibility that their employees are a threat, too. Insiders have legitimate access to organizational systems, allowing them to bypass many forms of detection. That access can be a problem whether the employee has malicious intent or not. An employee selling credentials poses a significant risk — and so does the worker who accidentally clicks on a suspicious link in their email.
- Whaling: An advanced phishing scam called whaling can be used to target and trick high-level employees. The hacker may request items such as money transfers, credentials, protected health information (PHI), or supplies, such as medicine. These tend to work better than regular phishing scams because they involve significant research on the victim and the person they’re impersonating.
- System vulnerabilities: All employees should install software updates and patches as soon as they come out. When you haven’t downloaded a necessary fix for a vulnerability, hackers have easy access to your network.
Healthcare Cybersecurity Best Practices and Tips
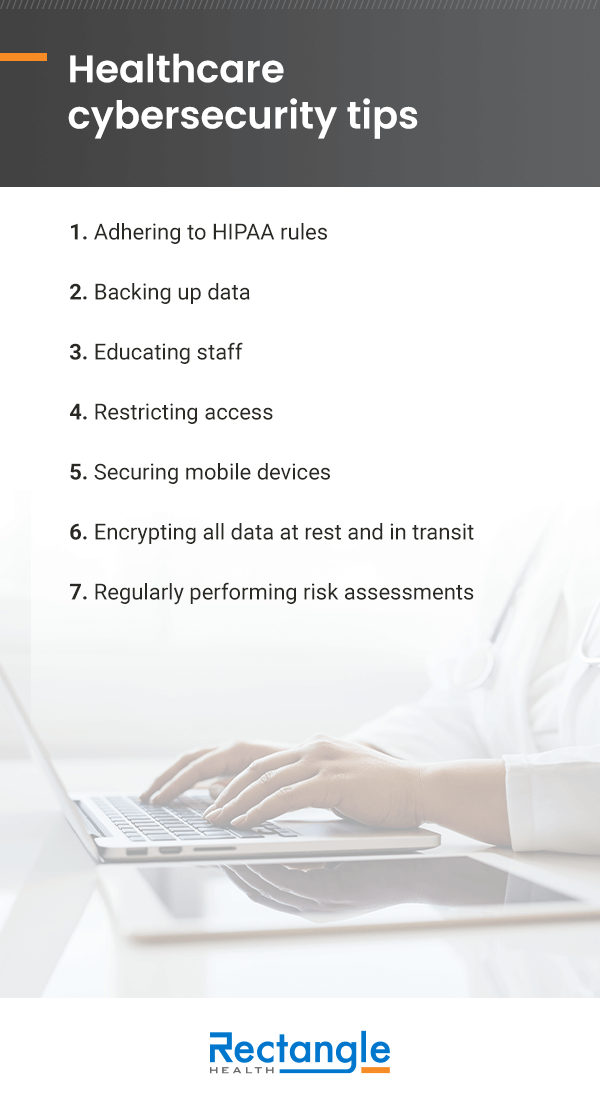
While every practice will have a unique digital setup, you can use a few general healthcare cybersecurity best practices to stay compliant and secure:
1. Adhering to HIPAA rules
HIPAA rules come into play across your organization. The two primary components are the Privacy Rule and Security Rule, which limit what information can be disclosed, how it can be used, and the standards and guidelines that dictate the handling of PHI. Those are wide-reaching topics, meaning HIPAA compliance must be considered in virtually every business process, from hiring a cleaning service to partnering with a cloud service provider.
2. Backing up data
All data recovery and contingency plans should ensure access to data should your system become unavailable. Backing up data can limit the impact of a breach because you can return to normal operations with fewer interruptions. This proactive security measure allows you to access data even when a malicious actor or natural disaster has compromised your servers.
To make recovery possible, data backups should be split up over multiple locations and separated from the main system. Of course, your backup must be HIPAA-compliant, as well.
3. Educating staff
As we’ve discussed, human error is the most common culprit for healthcare data breaches. Scams can be complex and hard to spot, but improved training can lessen the chance that employees will click on malicious links, overlook an inconsistency, or accidentally violate HIPAA policies.
Some areas of training that can help workers better anticipate and prepare for cybersecurity threats include:
- Spotting scams: Learning the signs of a phishing attempt, such as typos in email addresses, improper grammar, and other signals, can help employees better identify them and avoid violations.
- Being aware of suspicious employee activity: An effective way to catch internal threats is to encourage employees to keep an eye out for other workers. Someone may be able to simply correct a co-worker who learned a procedure incorrectly, or they could catch an employee intentionally releasing PHI for personal gain. In both cases, your employees make excellent eyes and ears around the practice.
- HIPAA requirements: Of course, HIPAA training is essential, but you’ll want to ensure employees understand the vulnerabilities of the software and equipment they use every day and how these potential threats affect HIPAA compliance.
4. Restricting access
The healthcare industry runs on the minimum necessary standard, where only people who need access to information can get it. This authorized access is a large part of that standard, as healthcare facilities need to ensure that only people with the authority and necessity to access data can do so. Employing technology such as two-factor authentication and complex password requirements can help limit unauthorized access.
5. Securing mobile devices
A weak link can put an entire system at risk — and that often involves the devices that hook up to your network. Technology like smartphones, laptops, tablets, and medical equipment can all be threats when you don’t manage them properly. One way to mitigate the threat of cybersecurity issues with healthcare devices is to enlist application controls, which specify a “whitelist” that grants access to authorized devices.
6. Encrypting all data at rest and in transit
It’s crucial to encrypt data during various stages, including the time it spends untouched in a server. By encrypting data in the “at rest” state, it’s protected during a breach. It’s also necessary to encrypt data while in transit, such as when data is being sent to someone outside of the network or throughout the facility.
7. Regularly performing risk assessments
No facility is the same. Therefore, risk assessments help qualify the areas that require your practice’s particular attention. Pursuing risk assessments also documents the measures you’ve taken to prevent data incidents. A comprehensive assessment should be performed regularly to keep pace with a changing business environment and an evolving technological landscape.
The Role of Electronic Payments in Healthcare Cybersecurity
As the healthcare industry embraces technology and the needs of consumers, electronic payment solutions are a key part of modern-day practice management. With both finances and HIPAA involved, you need to ensure your electronic payment provider abides by all regulatory requirements and continuously adapts to changes in the IT and healthcare industries. These providers have the important role of keeping both PHI and patient financial data secure.
For a long-trusted payment processor with robust cybersecurity and compliance tools, consider Rectangle Health. The Practice Management Bridge® platform allows you to accept a range of patient payments, including Text-to-Pay, tap to pay, digital wallets, Card on File, online payments, and payment plans. These options are available on a system that’s fully HIPAA compliant and utilizes finance industry protections like Point-to-Point Encryption (P2PE), Address Verification Systems (AVS), and EMV compliance for complete peace of mind.
References
- Cases Currently Under Investigation. (n.d.). U.S. Department of Health and Human Services Office for Civil Rights Complaint Portal Assistant. https://ocrportal.hhs.gov/ocr/breach/breach_report.jsf
- 2021 Data Breach Investigations Report (DBIR). (2021). Verizon. https://www.verizon.com/business/resources/reports/2021-data-breach-investigations-report.pdfx
- The Average Cost of a Healthcare Data Breach is Now $9.42 Million. (2021). HIPAA Journal. https://www.hipaajournal.com/average-cost-of-a-healthcare-data-breach-9-42-million-2021/
- How much does a data breach cost?. (2021). IBM. https://www.ibm.com/reports/data-breach
- Seh, A. H., Zarour, M., Alenezi, M., Sarkar, A. K., Agrawal, A., Kumar, R., & Ahmad Khan, R. (2020). Healthcare Data Breaches: Insights and Implications. Healthcare, 8(2), 133. doi:10.3390/healthcare802013




